Chapter 5: Q32E (page 167)
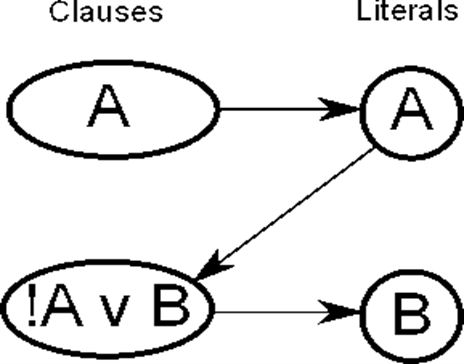
Question:Show how to implement the stingy algorithm for Horn formula satisfiability (Section 5.3) in time that is linear in the length of the formula (the number of occurrences of literals in it). (Hint: Use a directed graph, with one node per variable, to represent the implications.)
Short Answer
Answer:This challenge of determining whether such a combination of conceptual Horn sentences seems to be satisfiable or not is known as Horn-satisfiability. The indicated literals are the simplest representation of something like the Horn formula.